Cyberattacks are scary, because so few people actually know how to deal with them. The best response the average citizen has to contracting a computer virus is to Google how to fix the problem or to take their computer to a local expert who can cope with the issue.
That sort of response is not going to be enough to combat WannaCry, which is a form of "ransomware" that seized computers around the world over the weekend. Officials believe it is the largest online extortion scheme ever carried out, and the consequences may be dire if the public does not treat the threat as seriously as it should.
You don't need to run an IT department to be concerned about WannaCry or similar large-scale cyberattacks. Here's everything you need to know about it and how experts say you can best prevent future attacks.
What is WannaCry?
WannaCry is a widespread version of "ransomware," an attack typically attached to a virus infecting your computer. Once hackers trick people into clicking on a link containing the virus—traditionally using innocuous-looking emails for this goal, like fake bills or tax returns—they're able to send targeted messages at the user and mimic the cyber version of a hostage scenario.
After a computer is infected, ransomware threatens people with the loss of control and all their saved data if they don't act quickly to pay the hacker, usually in hard-to-trace currency like Bitcoins. Users have typically been asked to pay anywhere between $300 to $600 each for hackers to restore access to their computers and files.
This version of ransomware takes advantage of very specific flaws in old software. For example, computers using older editions of the Windows operating system that haven't been kept up to date with the latest security patches and drivers were vulnerable to WannaCry. Once WannaCry is on a computer, it fans out to any other computers linked to that machine or system and exploits the same weaknesses in the computer's security it used to latch onto the first one.
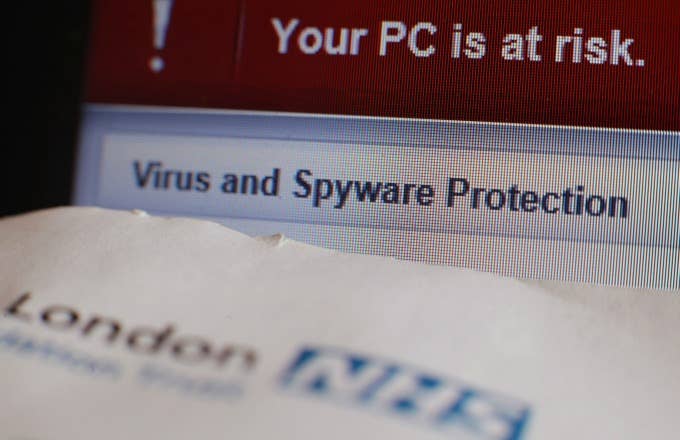
The screen of a computer being subjected to WannaCry may look something like this:
WannaCry fallout in the U.K.: canceled surgeries, exams and angry patients https://t.co/W9XK6clo9S pic.twitter.com/qqMLJmWlhn
How big is the problem?
This is a serious problem for personal computer use, particularly for those who don't consistently check for updates or pay much attention to patches when they come through. But the ability to spread rapidly to computers on one system leaves businesses and larger operations particularly susceptible to the attack.
Companies as big as FedEx were forced to acknowledge they'd been compromised by the first wave of attacks, and the impact of WannaCry caused many businesses to grind to a halt as they attempted to deal with the issue. The most notable of those stoppages was in hospitals throughout the United Kingdom, with medical staff forced to cancel any non-urgent appointments due to an inability to access any medical records on hospital computers.
statement from @NHSDigital on the #nhscyberattack. says 16 NHS organisations report they've been affected pic.twitter.com/OhB64UHQgk
The widespread nature of the attack makes it hard to pin down any exact figures, but the numbers we do have are troubling. Over 200,000 computers in 150 countries have reportedly been affected, and the BBC traced at least $38,000 paid to accounts linked to the attack.
Although statements from the UK's National Health Service and subsequent media reports insist the attacks are random rather than targeted, the hospital example in particular highlights the danger of WannaCry to the public.
Experts on the subject don't believe the indiscriminate nature of the crime makes it any better. Michael Gazeley, the director of cybersecurity firm Network Box, compared the attack to shooting into a crowd with a machine gun and hitting an old woman or a child with the bullets.
"You can't say you didn't mean to hit them," Gazeley said. "You shouldn't have been shooting into a crowd in the first place."
How much worse can it get?
The first wave of attacks was stopped (or at least slowed) by experts who discovered a "kill switch" built into the ransomware, and it allowed for remote disabling of the malware. Discoveries like these and increased awareness of the attack should help stop new computers from being infected by the original WannaCry bug. But the same researcher who discovered the kill switch warned that newer editions of the ransomware will probably not have the same flaw:
Version 1 of WannaCrypt was stoppable but version 2.0 will likely remove the flaw. You're only safe if you patch ASAP.
At least two new variations of the malware were discovered as of Monday morning, so this claim is not unfounded. The other concern is how many computers are laying dormant with the virus, which is something experts believe could spark further infection as the workforce returns to their computers this week.
"We've never seen anything like this," said Rob Wainwright, the director of the European Union's law enforcement agency Europol. "At the moment we are in the face of an escalating threat and the numbers are going up. I'm worried about how the numbers will continue to grow when people go to work and turn their machines on Monday morning."
How do you protect yourself from WannaCry?
The easiest solution to dealing with WannaCry is to do something companies have been begging their users to do for years—keep your devices up-to-date with the latest software as often and as quickly as you can. Hackers are always seeking ways to exploit new software, and the longer you stick with an outdated OS, the more likely it is to be exploited by wrongdoers.
One of the issues in the WannaCry attacks, however, is the public's reluctance to heed the advice of experts in the field. Ransomware has been a problem on some level for years, and cybersecurity teams have specifically recommended mass upgrades of hardware and software to avoid attacks like these. The National Health Service—the aforementioned healthcare provider devastated by the attacks—was told by regulators as far back as June 2016 to update their equipment in an effort to avoid similar attacks.
"Computer hardware and software that can no longer be supported should be replaced as a matter of urgency," read a document on the matter. In the same document, provided by the Care Quality Commission, it was revealed that a previous data breach cost one hospital upwards of £700,000, or roughly $900,000. This massive loss was sparked by a small mishap, which they traced to one employee clicking a bad link in an "unsafe email."
As with any computer vulnerability, the best thing you can do is to be vigilant in how you consume content online. Spam filters for emails are getting pretty good these days, but cyber criminals continue to work to find ways around whatever safeguards are put in place. Although experts are working around the clock to stop criminal efforts like these, savvy use of the Internet is the best first line of defense.
Brad Smith, Microsoft's President and Chief Legal Officer, emphasized the need for consumers to keep up with the times in a post released on the company's website.
"The fact that so many computers remained vulnerable two months after the release of a patch illustrates this aspect," said Smith. "As cybercriminals become more sophisticated, there is simply no way for customers to protect themselves against threats unless they update their systems."
Despite tech's dominance of our lives in 2017, the vast majority of people know very little about how the machines they use work. Until the public's knowledge of their tools catches up to the frequency with which they use them, attacks on the scale of the WannaCry outburst have the potential to be duplicated more frequently than you'd care to think about.